Injection refers to the process of adding cheat modules or code into a game process via an injector, thereby enabling cheating without modifying the original source code. On Android systems, this is typically achieved through methods such as SO injection, ptrace injection, and Zygote injection.
The Xposed Framework is a framework service that can influence application behavior (modify system settings) without modifying APKs. Based on it, numerous powerful Cheats can be developed.
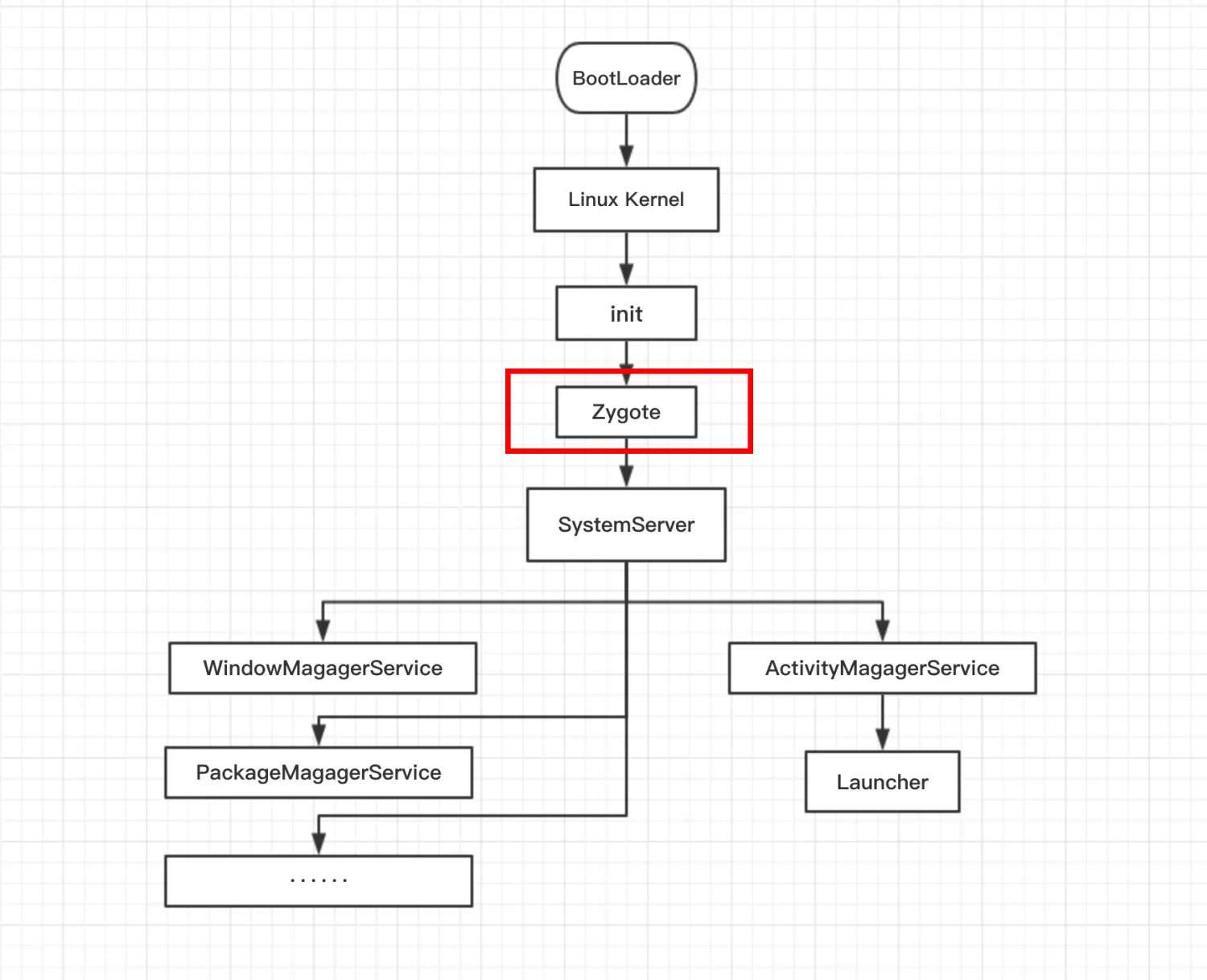
In the Android system, all application processes are spawned from the Zygote process. Xposed achieves its functionality by replacing the /system/bin/app_process executable to control the Zygote process. This causes it to load the Xposed framework's JAR file during system startup, thereby hijacking both the Zygote process and the Dalvik/ART virtual machines it creates.
After completing the injection, the Hook functionality of the Xposed framework can be utilized. This manifests as inserting custom code logic before or after the execution of target functions, thereby enabling the customization and modification of function behavior.
As an early open-source framework, Xposed's feature detection proved relatively straightforward. It was gradually replaced by the EdXposed framework, which further integrated Magisk compatibility and enhanced certain functionalities. This evolution ultimately gave rise to the more mainstream LSPosed framework.
The LSPosed framework leverages certain Magisk functionalities to achieve precise intervention at the ART layer without touching core system components, and includes built-in stealth capabilities to evade detection.

From the perspective of cheating principles, the LSPosed framework offers a more flexible and convenient modification approach. It enables alterations to game value modules and runtime logic without compromising the application's signature or integrity. Operation requires root access on the device, which can be provided by virtual frameworks or virtual machines, significantly lowering the barrier to entry.
To address the injection-based cheating risks faced by games, JikGuard has developed a specialized countermeasure strategy. This solution has been integrated into multiple popular games and has demonstrated outstanding protection capabilities.
Proactive Malicious Module Identification Mechanism
Unlike other security products on the market that require obtaining samples before combating Cheats, JikGuard's exclusive “Proactive Malicious Module Identification Mechanism” actively identifies suspicious modules. Combined with its online countermeasure capabilities, it enables proactive defense, significantly reducing the time required for Cheat detection and investigation.
Anti-Injector Functionality
Prohibits the use of Cheats such as Xposed and Frida, preventing malicious activities like modifying game memory after injection. Upon detection, the app will immediately crash.
Anti-Debugging Feature
Prevents Cheats developers from debugging the game, blocks static or dynamic analysis of the game, and triggers an immediate crash upon detection.
Security Environment Detection Capabilities
Unlike other products on the market, JikGuard employs deeper-level detection methods to accurately identify various risk environments such as virtual frameworks, virtual machines, rooted devices, jailbroken devices, and cloud phones, while providing customized crash prevention strategies.