Artificial intelligence (AI) has lowered the barrier to entry for both cyber attackers and cyber defenders.
During Infosecurity Europe 2024, cybersecurity platform provider SentinelOne will showcase how Purple AI, its new assistant tool for cybersecurity professionals, can help speed up the work of skilled analysts and democratize threat hunting for other cyber practitioners.
SentinelOne’s Demo at Infosecurity Europe
A ‘Man vs Machine’ Threat Hunt
Speaking to Infosecurity, Brett Taylor, SentinelOne’s senior engineering director for the UK and Ireland, shared what to expect from the ‘Man vs Machine’ demonstration.
He described it as a 30-minute live threat-hunting competition during which two back-to-back people, a skilled security operations analyst and either a customer or a SentinelOne commercial team member, operate on two different consoles in real time and try to narrow down as much information on a specific threat as possible.
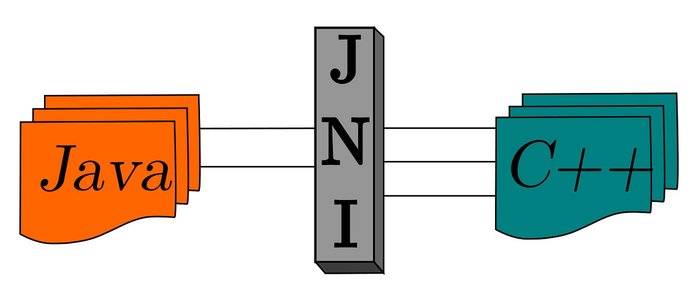
“The security engineer will use SentinelOne’s platform and our proprietary PowerQuery language, and the other person will use Purple AI and natural language to perform the same threat-hunting task. The first to get the wanted result wins,” explained Taylor.
A Real-Life Simulation
The case both competing people will work on consists of simulated data from a standard advanced persistent threat (APT) actor’s activity trying to infect a system with malware.
It will involve all the steps typical of a common APT group’s techniques, tactics and procedures (TTPs), including elements of evasion, persistence, lateral movement and process injection.
Both competitors' live threat hunting will be projected to an audience on a split screen in real-time.
“Usually, a skilled security operations center (SOC) analyst would get some notifications in the SentinelOne system, such as indicators of compromise (IOCs),” Taylor said.
“They would then use these as the first part of a query that they would write using our PowerQuery language, which allows them to ask questions around those IOCs and then pivot on the result sets returned by our engine,” he continued.
How AI can Democratize Threat Hunting
Embarking with a Purple AI-Enabled Threat Hunter
The non-skilled threat hunter will use the Purple AI dashboard. The dashboard allows users to analyze data from their endpoint, detection and response (EDR) solution.
First, using SentinelOne’s AI-powered product called ‘AI Security Analyst,’ they would ask a question in natural language – in English – about a potential threat. For instance: ‘Am I targeted by UNC1878?’
UNC1878 is the MITRE tracking identifier of a threat group that monetizes network access via the deployment of Ryuk ransomware.
“We use MITRE denominations for threat actors in our engine so that we avoid confusion between attributions from different security vendors,” Taylor noted.
Upon receiving this input, Purple AI would gather all telemetry associated with UNC1878 and other linked groups and show the results in another box, including a list of IOCs, IP addresses, hashes, and other elements related to UNC1878’s TTPs in the simulated system.
No tags.