Microsoft has warned retailers and restaurants of sophisticated gift card fraud which can cost victims up to $100,000 a day.
In a new Cyber Signals report, the tech giant highlighted a 30% rise in intrusion activity by the threat actor Storm-0539 between March and May 2024.
The group, which operates out of Morocco, focuses on compromising cloud and identity services in the criminal targeting of gift card portals linked to large retailers, luxury brands and well-known fast-food restaurants in.
Microsoft has observed Storm-0539 ramping up its activity in the build up to US holidays like the upcoming Memorial Day on May 30, 2024. It has observed a 30% rise in the group’s intrusion activity between March and May 2024.
There was also a 60% increase in the group’s intrusion activity between September and December 2023 to coincide with Thanksgiving, Black Friday and Christmas, Microsoft found.
Reconnaissance Used to Target Gift Card Creators
Storm-0539 uses deep reconnaissance and sophisticated cloud-based techniques to target gift card creators, similar to espionage campaigns by nation-state actors, Microsoft said.
The group has been active since late 2021 and focuses on attacking payment card accounts and systems.
Initially, it commonly compromised payment card data with point-of-sale (POS) malware. However, it evolved to targeting gift card portals as a result of industries hardening POS defenses, according to the report.
To conduct its initial reconnaissance, Storm-0539 attempts to infiltrate employees’ accounts at target organizations by sending smishing texts to personal and work mobile phones. It does this by accessing employee directories and schedules, contact lists and email inboxes.
Once an account is compromised, the attackers move laterally through the network, trying to identify the gift card business process and gather information on remote environments such as virtual machines, VPN connections, SharePoint and OneDrive resources.
Storm-0539 then uses this information to create new gift cards via compromised employee accounts. This allows them to redeem the value associated with those cards, sell the gift cards to other threat actors on black markets, or use money mules to cash out the gift cards.
Microsoft said it has seen examples of the threat actor stealing up to $100,000 a day at certain companies using this approach.
The group is able to maintain persistent access to compromised accounts by registering its own malicious devices to victim networks for subsequent secondary authentication prompts. This enables it to bypass multifactor authentication (MFA) protections.
Leveraging the Cloud to Remain Undetected
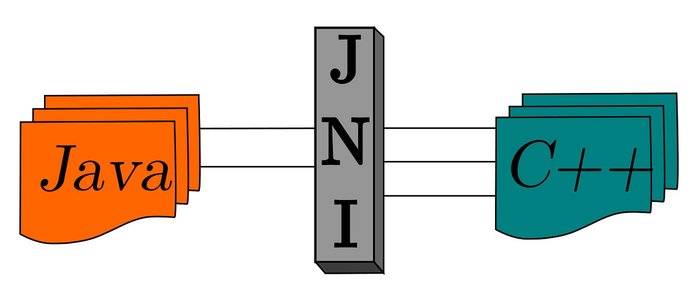
The report highlighted Storm-0539’s ability to leverage cloud resources to disguise themselves and their infrastructure while conducting such attacks.
The group presents itself as a legitimate organization to cloud providers to gain temporary application, storage, and other initial free resources for their attack activity.
As part of this effort to appear legitimate, it creates websites that impersonate charities, animal shelters, and other nonprofits in the US via typosquatting – whereby a common misspelling of an organization’s domain is registered.
Microsoft believes Storm-0539 carries out extensive reconnaissance into the federated identity service providers at targeted companies to convincingly mimic the user sign-in experience. This includes the appearance of the adversary-in-the-middle (AiTM) page and the use of registered domains that closely match legitimate services.
No tags.