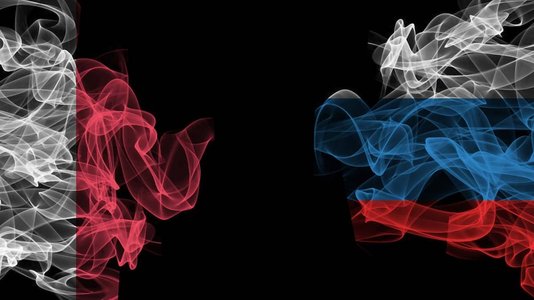
Researchers from cybersecurity firm ESET found that a recent cyber espionage campaign using the open-source malware XploitSPY targeted Android users in India and Pakistan.
The campaign, which ESET named ‘eXotic Visit,’ was active between November 2021 and the end of 2023.
ESET researchers observed around 380 victims of the campaign.
Although they were unable to attribute the campaign to a known adversary, ESET researchers referred to the threat actors as ‘Virtual Invaders.’
Decoding eXotic Visit
How Victims Get Compromised with XploitSPY
To lure their victims into downloading the XploitSPY malware, Virtual Invaders bundled it together with mobile applications, primarily messaging apps.
Most of these apps are fake but functioning messaging apps. The threat actors behind the campaign started providing these malicious apps on dedicated websites before offering some on the Google Play Store as well.
XploitSPY is a Remote Access Trojan (RAT) that was uploaded to GitHub as early as April 2020 by a user named RaoMK, who was allegedly associated with an Indian cyber security solutions company called XploitWizer.
XploitSPY is based on L3MON, a now-defunct open-source Android RAT inspired by AhMyth.
XploitSPY’s Espionage Capabilities
Once a victim has installed a compromised app, the XploitSPY payload inside can extract various types of data, such as:
- Contact lists and files
- Call logs
- A list of installed apps
- A list of surrounding Wi-Fi networks
- The device’s GPS location
- The names of files listed in specific directories related to the camera, downloads, and various messaging apps such as Telegram and WhatsApp
XploitSPY also allows the threat actors to perform malicious actions on the victim’s phone. These include:
- Sending SMS messages
- Taking pictures using the camera
- Recording audio from the device’s surroundings
- Intercepting notifications received for WhatsApp, Signal and any other notification that contains the string ‘new messages’
If specific filenames are identified as being of interest, they can subsequently be extracted from these directories via an additional command from ngrok, Virtual Invaders’ command and control (C2) server.
“Interestingly, the implementation of the chat functionality integrated with XploitSPY is unique; we strongly believe that this chat function was developed by the Virtual Invaders group,” the researchers explained.
An Evolving Campaign
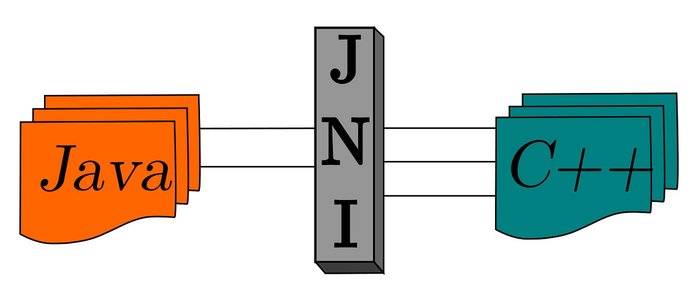
The malware also uses a native library, whose purpose is not to improve performance and access system features, as is often the case in Android app development, but to hide sensitive information, like the addresses of the C2 servers, making it harder for security tools to analyze the app.
The campaign has evolved over the years to include obfuscation, emulator detection and hiding of C2 addresses.
No tags.